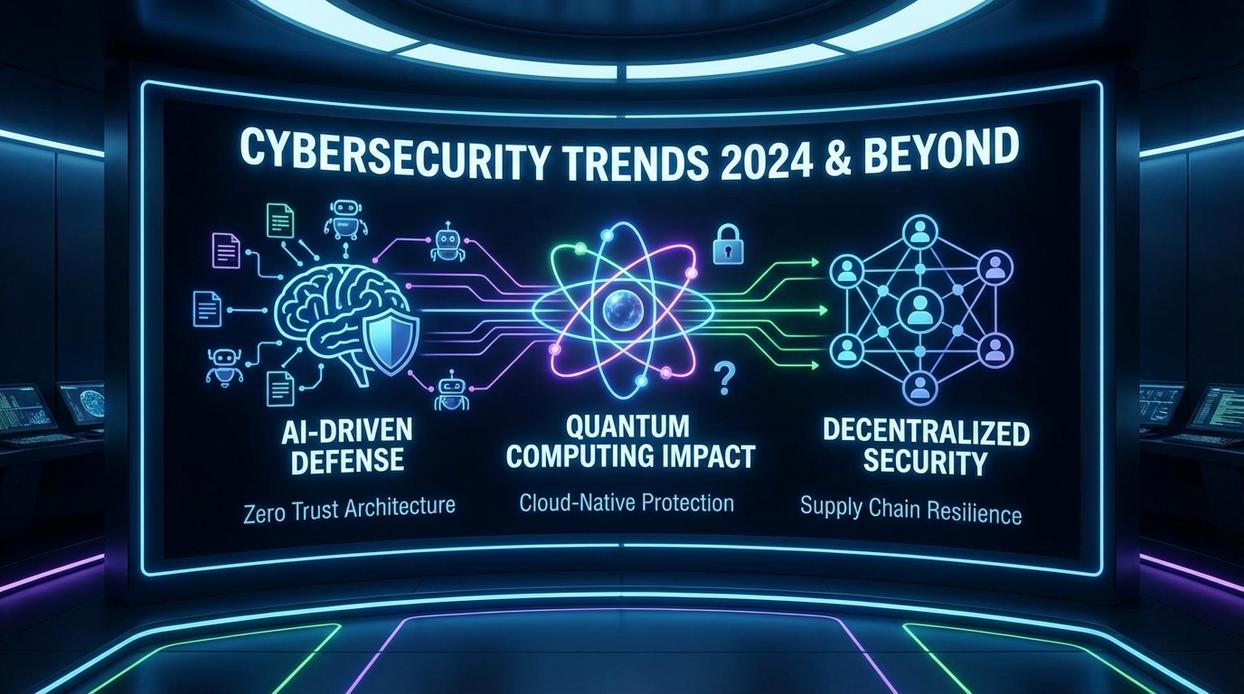
Data breaches cost organizations over $4.5 million on average last year—a staggering figure that underscores how relentless and expensive cybercrime has become. As businesses expand across cloud platforms, remote networks, and connected devices, the digital attack surface grows exponentially, rendering traditional perimeter defenses increasingly obsolete. Staying ahead of modern threats is no longer optional; it’s a core business imperative. This analysis cuts through the noise to deliver a clear, actionable breakdown of the most important cybersecurity industry trends shaping defense strategies today and tomorrow, helping you understand where the sector stands—and where it’s headed next.
The AI Arms Race: Offensive vs. Defensive Artificial Intelligence
Last year, I opened what looked like a routine security alert and realized it was written better than most marketing emails. That was my first brush with AI-generated phishing.
The Dual Nature of AI
Artificial Intelligence is a double-edged sword in cybersecurity. The same algorithms that help defenders detect anomalies also help attackers craft hyper-personalized lures.
Offensive AI
Threat actors now use AI to generate hyper-realistic phishing campaigns, automatically discover vulnerabilities, and build polymorphic malware that mutates to evade signature-based detection. It is automation at scale, and it is frighteningly efficient.
Defensive AI
Security teams fight back with Machine Learning models for advanced threat intelligence, anomaly detection, and Security Orchestration, Automation, and Response (SOAR) that triage alerts at machine speed. In my own lab, I watched an AI system isolate suspicious traffic in seconds, something that once took hours of manual log review.
How the arms race plays out:
- Attackers iterate faster.
- Defenders automate responses.
- Both sides learn from data.
Some argue AI is overhyped, that human intuition will always outsmart code. I disagree. What I see in cybersecurity industry trends in the section once exactly as it is given is a clear acceleration toward autonomous systems.
The practical takeaway is simple: adopt AI for defense, and learn how to defend against AI-powered attacks. Complacency is the real vulnerability. Whether you manage a home network or an enterprise stack, understanding this duality is no longer optional. AI is already on both sides of the keyboard. Prepare accordingly and stay vigilant.
Cloud Security Matures: The Era of CNAPP and Shared Fate
Cloud sprawl sounds harmless—until you’re juggling AWS, Azure, containers, Kubernetes clusters, and dozens of microservices. Each layer adds complexity, and with complexity comes risk. Misconfigured storage buckets, over-permissioned identities, and unpatched container images are now common breach paths (IBM’s 2023 Cost of a Data Breach Report found misconfigurations among leading causes). In other words, the modern cloud can feel like a house with too many unlocked doors.
So what’s the fix? Enter Cloud-Native Application Protection Platforms (CNAPP)—a unified security approach that combines CSPM (Cloud Security Posture Management) and CWPP (Cloud Workload Protection Platforms). Instead of separate dashboards, CNAPP offers one view across development and production. Practically speaking, that means you can scan infrastructure-as-code templates before deployment, detect runtime threats in containers, and prioritize risks in a single workflow.
Next, shift-left security moves checks into your CI/CD pipeline. For example, integrate image scanning into GitHub Actions so vulnerable packages fail the build automatically (pro tip: treat failed scans like failed tests—non-negotiable).
Finally, the Shared Responsibility Model is evolving into Shared Fate, where providers offer secure-by-default settings and proactive alerts. As cybersecurity industry trends show, collaboration—not isolation—is the future.
Identity as the New Perimeter: The Zero Trust Mandate
Back in 2019, most organizations still relied on a hardened network edge—firewalls, VPNs, and on-prem data centers. Then remote work accelerated almost overnight in 2020. SaaS applications multiplied, employees logged in from personal devices, and the traditional perimeter quietly dissolved. In other words, the “castle-and-moat” model failed because there was no castle anymore.
That shift forced a rethink. Enter Zero Trust—a security model built on “never trust, always verify.” Instead of assuming users inside the network are safe, Zero Trust demands proof at every access point. Micro-segmentation (dividing networks into smaller, isolated zones) limits lateral movement. The principle of least privilege ensures users only access what they absolutely need. And continuous authentication checks identity repeatedly, not just at login (yes, even if that feels mildly annoying).
Some critics argue Zero Trust is overkill—too complex, too disruptive. Fair. Implementation can take months, even years. However, according to IBM’s 2023 Cost of a Data Breach Report, breaches average $4.45 million globally. Suddenly, “overkill” sounds prudent.
Modern Identity and Access Management (IAM) underpins everything. Multi-factor authentication (MFA) and Privileged Access Management (PAM) reduce risk from stolen credentials—the leading attack vector cited in cybersecurity industry trends in the section once exactly as it is given.
Ultimately, Zero Trust isn’t a product you install. It’s an ongoing strategy to remove implicit trust—everywhere. For broader context, explore top emerging technology trends shaping the future of computing.
Preparing for “Y2Q”: The Post-Quantum Cryptography Imperative
Think of today’s encryption like a really strong padlock. Classical computers struggle to crack it. But future quantum computers? They’re less “lockpick” and more “teleport behind the door.” Algorithms like RSA and ECC (Elliptic Curve Cryptography, a method securing everything from banking apps to game logins) could be broken once large-scale quantum machines arrive.
Now for the spooky part: Harvest Now, Decrypt Later. Adversaries are already collecting encrypted data today, betting they can unlock it tomorrow. Sensitive health records, trade secrets, even your old cloud backups—nothing says “surprise” like decrypted data from 2024.
Meanwhile, the National Institute of Standards and Technology (NIST) is standardizing quantum-resistant algorithms to prepare for this shift.
Some argue quantum threats are decades away. Maybe. But cybersecurity industry trends show long transition cycles.
Call to Action:
- Build a crypto-inventory
- Identify critical data
- Plan your Post-Quantum Cryptography migration
(Pro tip: migrations take years, not weekends.)
Building a Resilient and Proactive Security Posture
The future of security is intelligent (AI), integrated (CNAPP), identity-focused (Zero Trust), and forward-looking (PQC). These trends are not optional upgrades—they are direct responses to a threat landscape that grows more dynamic and complex every day. A reactive or static defense is no longer enough; attackers evolve too quickly.
You came here to understand how to build a security posture that can withstand modern threats. Now you know that true resilience requires continuous adaptation, proactive threat hunting, and strategic investment in emerging frameworks.
If your defenses feel outdated or fragmented, now is the time to act. Start assessing gaps, prioritize integration, and commit to a proactive strategy today to stay ahead of tomorrow’s threats.


 Content Strategist & Linux Gaming Researcher
Ask Anitaca Russelloren how they got into linux performance tweaks and you'll probably get a longer answer than you expected. The short version: Anitaca started doing it, got genuinely hooked, and at some point realized they had accumulated enough hard-won knowledge that it would be a waste not to share it. So they started writing.
What makes Anitaca worth reading is that they skips the obvious stuff. Nobody needs another surface-level take on Linux Performance Tweaks, Proton Compatibility Insights, Linux Setup Optimization Tips. What readers actually want is the nuance — the part that only becomes clear after you've made a few mistakes and figured out why. That's the territory Anitaca operates in. The writing is direct, occasionally blunt, and always built around what's actually true rather than what sounds good in an article. They has little patience for filler, which means they's pieces tend to be denser with real information than the average post on the same subject.
Anitaca doesn't write to impress anyone. They writes because they has things to say that they genuinely thinks people should hear. That motivation — basic as it sounds — produces something noticeably different from content written for clicks or word count. Readers pick up on it. The comments on Anitaca's work tend to reflect that.
Content Strategist & Linux Gaming Researcher
Ask Anitaca Russelloren how they got into linux performance tweaks and you'll probably get a longer answer than you expected. The short version: Anitaca started doing it, got genuinely hooked, and at some point realized they had accumulated enough hard-won knowledge that it would be a waste not to share it. So they started writing.
What makes Anitaca worth reading is that they skips the obvious stuff. Nobody needs another surface-level take on Linux Performance Tweaks, Proton Compatibility Insights, Linux Setup Optimization Tips. What readers actually want is the nuance — the part that only becomes clear after you've made a few mistakes and figured out why. That's the territory Anitaca operates in. The writing is direct, occasionally blunt, and always built around what's actually true rather than what sounds good in an article. They has little patience for filler, which means they's pieces tend to be denser with real information than the average post on the same subject.
Anitaca doesn't write to impress anyone. They writes because they has things to say that they genuinely thinks people should hear. That motivation — basic as it sounds — produces something noticeably different from content written for clicks or word count. Readers pick up on it. The comments on Anitaca's work tend to reflect that.